A Lightweight and Robust Access Control Protocol for IoT-Based e-Healthcare Network
A Lightweight and Robust Access Control Protocol for IoT-Based e-Healthcare Network
OUR PROPOSED PROJECT TITLE:
Chaotic Key-Based Secure Data Access Protocol for IoT Healthcare
IEEE BASE PAPER ABSTRACT:
Internet of Things (IoT) devices are crucial components in e-healthcare networks. It enables remote patient health monitoring and facilitates seamless communication among medical sensors, wearable devices, and healthcare providers through public communication channels. Despite these advantages, the use of public communication among medical sensors in e-healthcare networks introduces critical challenges, such as vulnerability to impersonation, physical capture, and ephemeral secret leakage, particularly in resource-constrained environments. In recent years, various access control protocols have been developed to mitigate these risks. However, these protocols often fail to ensure robust security while incurring significant communication and computation overhead. To overcome these limitations, we propose a lightweight and robust access control protocol for IoT-based e-healthcare networks using chaotic maps. We propose a novel protocol that integrates a PUF-based mechanism to mitigate the challenges of physical tampering and cloning attacks in e-healthcare networks. It leverages the inherent uniqueness of PUF and enhances security through the high-entropy properties of chaotic maps. We analyze the proposed protocol informally, which confirms that it significantly bolsters efficiency and security. We also validate the security using the Random or Real (RoR) model. Moreover, we verify the security of the proposed protocol using Scyther. These analyses highlight that the proposed protocol offers robust resistance to numerous attacks, such as impersonation, physical capture, and ephemeral secret leakage. Moreover, we also compare it with existing and relevant protocols. The comparative analysis showcases its superior performance. Notably, the proposed authentication protocol significantly reduces 46.84% computational overhead and decreases 31.30% communication overhead, underscoring its enhanced performance and resource efficiency.
PROJECT OUTPUT VIDEO:
OUR PROPOSED PROJECT ABSTRACT:
The rapid advancement of Internet of Things (IoT) technologies has significantly transformed the healthcare sector by enabling continuous patient monitoring, real-time diagnosis, and remote medical assistance. IoT-based e-Healthcare networks integrate medical sensing devices, cloud platforms, and healthcare professionals to deliver efficient and timely medical services. However, the sensitive nature of physiological data such as ECG, EEG, SpO₂, blood pressure, and body temperature raises serious concerns regarding data confidentiality, secure transmission, authentication, and controlled access. Unauthorized disclosure or manipulation of medical records can lead to critical risks, making lightweight yet robust access control mechanisms essential for secure e-Healthcare environments.
The need for a secure access control protocol arises from the increasing deployment of wearable and remote sensing devices that continuously generate patient health data. These devices operate in resource-constrained environments, requiring security solutions that are computationally efficient while still ensuring strong protection. Furthermore, healthcare systems involve multiple stakeholders such as patients, doctors, and cloud administrators, each requiring different levels of access privileges. Ensuring that only authorized medical professionals can view decrypted patient data, while even cloud administrators are restricted from accessing original records, is crucial for preserving privacy, trust, and regulatory compliance in digital healthcare systems.
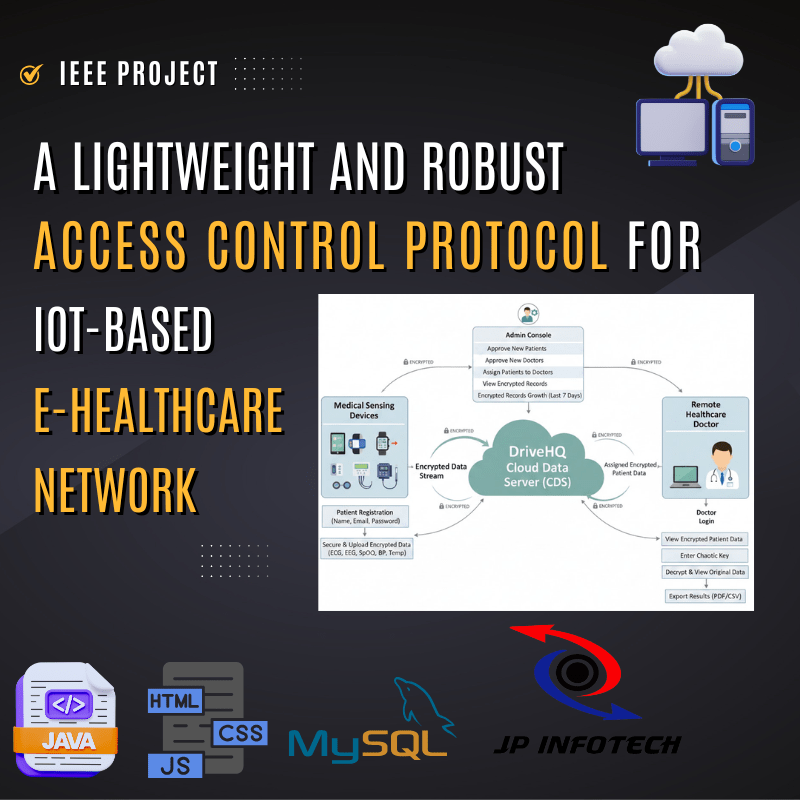
To address these challenges, the project titled “A Lightweight and Robust Access Control Protocol for IoT-Based e-Healthcare Network” has been developed using Java as the core programming language, with JSP, CSS, and JavaScript for the frontend interface and MySQL as the database. The system architecture is designed around three primary entities: Cloud Data Server (CDS), Remote Healthcare Doctor, and Medical Sensing Devices.
Overall, the developed system delivers a lightweight, secure, and efficient access control protocol tailored for IoT-enabled e-Healthcare networks. By combining encryption, role-based authorization, chaotic key decryption, and cloud analytics, the project ensures secure medical data handling while supporting scalable and privacy-preserving remote healthcare services.
EXISTING SYSTEM:
- In the existing IoT-based e-Healthcare environment, several authentication and access control protocols have been proposed to secure communication between medical sensing devices, cloud servers, and healthcare providers. These systems primarily focus on enabling remote patient monitoring and secure data exchange over public communication channels. Traditional solutions employ cryptographic techniques such as symmetric encryption, hash functions, elliptic curve cryptography (ECC), digital signatures, and biometric-based authentication to ensure confidentiality and integrity of medical data. Some frameworks also incorporate two-factor authentication and certificate-based verification to strengthen user validation processes.
- In the existing system some system have introduced blockchain-based decentralized access control architectures to enhance transparency and tamper-proof logging in e-Healthcare systems. Blockchain ensures immutable data storage and secure sharing of medical records among stakeholders. However, these systems often fail to address real-time authentication and key agreement requirements for IoT medical devices. Additionally, blockchain operations impose high computational and storage overhead, making them unsuitable for resource-constrained sensing devices such as wearable health monitors.
- In Other existing approaches include authentication and key agreement protocols designed for Wireless Body Area Networks (WBANs). These protocols utilize lightweight operations such as XOR functions, hash computations, and Physical Unclonable Functions (PUFs) to provide device authentication. While they offer efficient short-range communication security, their applicability is limited to localized WBAN environments and does not extend effectively to large-scale cloud-integrated e-Healthcare infrastructures. Furthermore, such systems remain vulnerable to desynchronization issues, impersonation attacks, and ephemeral secret leakage when deployed in broader IoT healthcare ecosystems.
- Privacy-enhanced transmission mechanisms have also been explored using forward-secure signatures and time-lock puzzles to protect stored patient information from retrospective exposure. Although these methods improve data confidentiality, they do not sufficiently emphasize efficient mutual authentication and dynamic session key establishment. As a result, IoT medical devices operating under these frameworks remain susceptible to threats such as man-in-the-middle attacks and unauthorized access.
- Overall, the existing systems suffer from multiple security and performance limitations. Many protocols are unable to provide robust protection against impersonation, physical capture, cloning, and secret leakage attacks. In addition, they often incur high communication and computational overhead, which is impractical for low-power medical sensing devices. The lack of lightweight yet comprehensive authentication mechanisms highlights the need for more secure, scalable, and resource-efficient access control protocols tailored specifically for IoT-based e-Healthcare networks.
DISADVANTAGES OF EXISTING SYSTEM:
- High Computational Overhead: In the existing access control and authentication protocols in IoT-based e-Healthcare systems rely on complex cryptographic operations such as blockchain processing, elliptic curve cryptography, and digital signatures. These techniques require substantial processing power and memory. Since medical sensing devices are resource-constrained, executing such heavy computations leads to increased latency, faster battery depletion, and reduced device efficiency.
- Excessive Communication Overhead: In the existing system security frameworks often involve multiple rounds of message exchanges for authentication and key agreement. The transmission of large cryptographic parameters over public channels increases bandwidth consumption and network congestion. This overhead affects real-time health monitoring, where timely delivery of patient data is critical.
- Vulnerability to Impersonation Attacks: In the existing system, protocols fail to provide strong mutual authentication between medical devices and servers. Attackers can forge identities or replay intercepted messages to gain unauthorized access. This weakness allows malicious entities to impersonate legitimate patients, doctors, or devices within the healthcare network.
- Susceptibility to Physical Capture and Device Tampering: IoT medical sensors are often deployed in open or wearable environments, making them physically accessible to adversaries. Existing systems that depend on stored cryptographic keys are highly vulnerable – attackers can extract secret parameters through hardware tampering, leading to full system compromise.
- Ephemeral Secret Leakage Risks: In the existing system, many authentication schemes do not adequately protect temporary session parameters. If ephemeral secrets (such as session nonces or temporary keys) are exposed, attackers can reconstruct session keys, decrypt medical data, or launch replay attacks, thereby violating patient privacy.
- Lack of Scalability for Cloud-Integrated Healthcare: In the existing system, Protocols designed for localized environments like Wireless Body Area Networks (WBANs) are not scalable to large cloud-based e-Healthcare infrastructures. They fail to support long-range communication, multi-user access control, and large-scale patient monitoring systems.
- Exposure to Desynchronization Attacks: In several existing schemes, authentication relies on synchronized parameters between devices and servers. Communication failures or message loss can break synchronization, causing legitimate devices to be rejected and disrupting healthcare services.
- Inadequate Protection Against Man-in-the-Middle Attacks: In the existing system, without strong session key establishment and real-time verification, attackers can intercept and modify transmitted medical data. This leads to false diagnosis, incorrect treatment decisions, and compromised system integrity.
- Limited Privacy and Anonymity Preservation: In the existing system, some traditional access control mechanisms transmit static identities or traceable parameters over public channels. This enables adversaries to track patient activities, violating anonymity and confidentiality requirements in healthcare systems.
- Storage Overhead and Key Management Complexity: Existing systems often require storing multiple cryptographic keys, certificates, and verifier tables. Managing, updating, and securing these parameters increases storage burden on constrained devices and complicates system administration.
PROPOSED SYSTEM:
- The proposed system introduces a Lightweight and Robust Access Control Protocol for IoT-Based e-Healthcare Networks designed to ensure secure authentication, controlled data access, and protected communication among healthcare entities. The architecture is structured to support remote patient monitoring while preserving the confidentiality of sensitive medical information transmitted through public communication channels. The protocol integrates lightweight cryptographic operations with advanced security primitives to establish a secure framework suitable for resource-constrained IoT medical environments.
- The proposed system presents a secure and structured access control framework for an IoT-based e-Healthcare network that operates through three primary entities: the Cloud Data Server (CDS), Remote Healthcare Doctor, and Medical Sensing Devices. The system is designed to support secure patient registration, authenticated medical data transmission, controlled doctor access, and encrypted cloud storage within a centralized healthcare monitoring environment. Each entity performs specific roles that collectively enable remote patient monitoring and protected medical data management.
- In the medical sensing devices module, patient registration is carried out by entering personal credentials such as patient name, email ID, and password. Once the registration details are submitted, they are forwarded to the Cloud Data Server for administrative verification. The cloud administrator reviews the request and approves legitimate users before granting system access. A similar registration and approval workflow is followed for remote healthcare doctors. Doctors must submit their professional details through the system, and only after administrative approval are they authorized to log in and access patient data.
- After successful login, medical sensing devices function as the primary data acquisition unit of the system. Patients or healthcare operators input physiological sensor readings such as ECG, EEG, SpO₂ levels, blood pressure, and body temperature. Once these values are entered, the data undergoes a secure encryption process. By selecting the “secure and upload” option, the encrypted health records are transmitted and stored in the integrated DriveHQ cloud storage environment. This ensures that sensitive physiological information is uploaded in protected form rather than plain text.
- On the remote healthcare doctor side, authenticated doctors can log in to the system to review patient information. However, access is strictly controlled through administrative assignment. The Cloud Data Server assigns specific patients to specific doctors, and only those mapped relationships are authorized for viewing. When doctors access patient records, the medical values appear in encrypted format. To interpret the actual readings, the doctor must provide a valid chaotic key. Upon entering the correct key, the system decrypts the data, allowing the doctor to view the original sensor-generated medical values. The doctor is also provided with functionality to export patient reports and decrypted results for clinical documentation and future reference.
- The Cloud Data Server acts as the central administrative and data governance unit of the entire system. It is responsible for approving patient registrations, verifying and approving doctor accounts, and assigning patients to respective healthcare professionals. The CDS maintains all uploaded medical records in encrypted format. Even cloud administrators are restricted from viewing the original decrypted health values, ensuring strict data confidentiality within the storage layer.
- In addition to administrative controls, the Cloud Data Server incorporates an analytics module for monitoring system activities. The analytics dashboard presents graphical insights such as user-based ratio analysis, approval workflow statistics, and encrypted medical record growth over the previous seven days. These visual analytics assist in tracking system utilization, registration trends, and data storage expansion while maintaining encryption protection across all stored datasets.
- Overall, the proposed system establishes a multi-entity IoT e-Healthcare environment where patient sensing devices capture medical data, cloud servers manage authentication and storage, and remote doctors access encrypted patient information through controlled authorization and key-based decryption mechanisms.
ADVANTAGES OF PROPOSED SYSTEM:
- Secure Patient Data Transmission: The proposed system ensures that all physiological data collected from medical sensing devices such as ECG, EEG, SpO₂, blood pressure, and body temperature are encrypted before being transmitted to the cloud. This prevents unauthorized interception and protects sensitive patient health information during communication.
- Controlled Access to Medical Records: In the proposed system, access to patient data is strictly regulated through administrative assignment. Only doctors who are officially mapped to specific patients can view their records. This controlled authorization mechanism prevents unauthorized healthcare personnel from accessing confidential medical information.
- Multi-Level Authentication Mechanism: The proposed framework incorporates registration approval for both patients and doctors. Administrative verification ensures that only legitimate users are allowed into the system, strengthening overall access control and preventing fraudulent registrations.
- Chaotic Key-Based Decryption Security: Even after login, doctors cannot directly view original medical values. They must provide a valid chaotic key to decrypt encrypted patient data. This additional cryptographic layer enhances confidentiality and ensures that only authorized medical professionals can interpret clinical readings.
- Data Confidentiality in Cloud Storage: In the proposed system, all patient records stored in the Cloud Data Server remain in encrypted format. Even cloud administrators are unable to view the original medical values. This design preserves end-to-end privacy and protects against insider threats at the storage level.
- Secure Cloud Integration: The integration of DriveHQ cloud storage enables secure uploading, centralized management, and reliable backup of medical data. It supports protected remote access while maintaining encryption throughout storage and retrieval processes.
- Efficient Remote Patient Monitoring: In the proposed system, doctors can remotely monitor patient health conditions without requiring physical presence. This supports telemedicine services, continuous monitoring, and faster medical response for patients located in distant areas.
- Patient–Doctor Mapping Flexibility: In the proposed system, the Cloud Data Server provides an assignment mechanism where administrators can map patients to specific doctors. This structured allocation improves care coordination and ensures that each patient’s data is handled by the appropriate specialist.
- Exportable Medical Reports: In the proposed system, Doctors have the capability to export decrypted patient records and diagnostic results. This feature supports medical documentation, treatment planning, second opinions, and long-term clinical record maintenance.
- Administrative Monitoring and Analytics: In the proposed system, the analytics dashboard in the Cloud Data Server provides visual insights such as user ratio graphs, approval workflows, and encrypted record growth over the last seven days. These analytics assist administrators in monitoring system usage and operational trends.
- Lightweight and Practical Deployment: The proposed system is designed to operate efficiently with IoT medical sensing devices, making it suitable for real-time healthcare environments where quick data capture and secure transmission are essential.
- Enhanced Privacy Preservation: By combining encryption, controlled assignment, and key-based decryption, the system maintains strong privacy protection for patient identities and medical records across all entities.
SYSTEM REQUIREMENTS:
HARDWARE REQUIREMENTS:
- System : Pentium i3 Processor.
- Hard Disk : 20 GB.
- Monitor : 15’’ LED.
- Input Devices : Keyboard, Mouse.
- Ram : 8 GB.
SOFTWARE REQUIREMENTS:
- Operating system : Windows 10/11.
- Coding Language : Java.
- Frontend : JSP, CSS, JavaScript.
- JDK Version : JDK 23.0.1.
- IDE Tool : Apache Netbeans IDE 24.
- Tomcat Server Version : Apache Tomcat 9.0.84
- Database : MYSQL 8.0.
REFERENCE:
Zahid Ghaffar, Wen-Chung Kuo, Khalid Mahmood, Tayyaba Tariq, Salman Shamshad, Ashok Kumar Das, and Mohammed J. F. Alenazi, “A Lightweight and Robust Access Control Protocol for IoT-Based e-Healthcare Network”, IEEE TRANSACTIONS ON MOBILE COMPUTING, VOL. 24, NO. 9, SEPTEMBER 2025.